Introduction
PowerShell is one of the most widely used tools in Windows for automation, scripting, and system administration. Among its many advanced features, one of the most powerful yet least understood is the PowerShell Get-Content Stream.
The PowerShell Get-Content Stream allows users to read hidden data stored inside files using Alternate Data Streams. These streams are not visible through normal file browsing methods, which makes them useful for storing metadata, system information, and hidden content.
In simple terms, the PowerShell Get-Content Stream gives access to hidden layers inside a file that are normally invisible to users.
Understanding File Streams
To fully understand the PowerShell Get-Content Stream, it is important to first understand how file streams work in Windows.
A stream is an additional data layer inside a single file. While most files contain only visible content, Windows NTFS file systems allow multiple hidden streams to exist within the same file.
These hidden streams are called Alternate Data Streams (ADS). The main stream holds visible data, while secondary streams store hidden or additional information.
When using the PowerShell Get-Content Stream, users specifically target these hidden streams instead of the visible file content.
What Are Alternate Data Streams
Alternate Data Streams are a built-in feature of the NTFS file system. They were originally introduced for compatibility reasons but later became useful for advanced file handling and data storage.
In a normal file, such as a text document, only one visible stream is shown. However, NTFS allows multiple hidden streams to exist without changing the file’s appearance.
For example, a file can contain visible content, hidden metadata, and system-related information all at the same time. This makes the PowerShell Get-Content Stream a powerful tool for accessing deeper file layers.
| Feature | Details |
|---|---|
| Name | PowerShell Get-Content Stream |
| Tool | PowerShell |
| Purpose | Reads hidden file data (Alternate Data Streams) |
| Use | Security, forensics, system administration |
| File Support | NTFS file system only |
| Data Type | Hidden / alternate file streams |
| Visibility | Not shown in normal File Explorer |
| Users | IT admins, security experts, developers |
How It Works
The PowerShell Get-Content Stream works by allowing PowerShell to target a specific stream inside a file.
Instead of reading only the default visible content, it can access hidden streams directly. This gives users full control over what part of the file they want to inspect.
The process usually involves creating a file, adding hidden data into a stream, and then reading that stream using PowerShell commands. The PowerShell Get-Content Stream makes this process simple and direct for administrators and security professionals.
Syntax and Usage
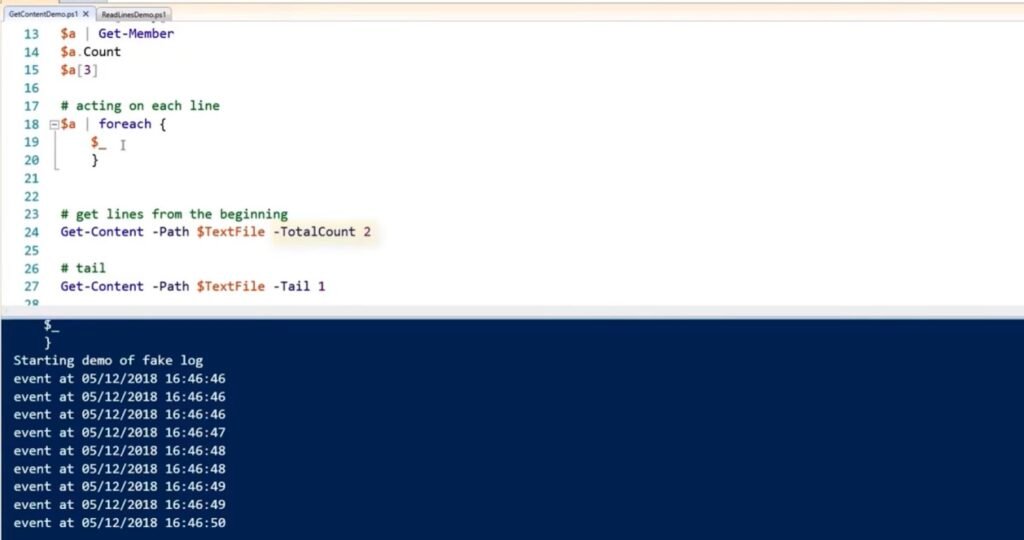
The syntax for using streams in PowerShell is simple and flexible. It requires specifying both the file path and the stream name.
This allows users to switch between visible and hidden content easily. If no stream is specified, PowerShell automatically reads the default visible content.
This flexibility is one of the reasons the PowerShell Get-Content Stream is widely used in advanced file analysis.
Creating Hidden Streams
Hidden streams are created by attaching additional data to an existing file without changing its visible content.
A normal file might contain simple text that users can read. However, extra hidden data can be added into a separate stream that remains invisible in standard file explorers.
Once created, these hidden streams remain part of the file and can only be accessed using tools like the PowerShell Get-Content Stream.
This separation of visible and hidden data makes streams extremely useful in advanced computing environments.
Reading Hidden Data
When using the PowerShell Get-Content Stream, reading hidden data becomes straightforward. Instead of displaying the main file content, PowerShell retrieves information stored in the selected stream.
This is especially useful when files contain logs, metadata, or hidden instructions that are not visible through normal viewing methods.
The ability to extract hidden information makes the PowerShell Get-Content Stream an essential tool for IT professionals working with complex file systems.
Real-World Use Cases
The PowerShell Get-Content Stream is widely used in cybersecurity, system administration, and digital forensics.
In cybersecurity, professionals use it to detect hidden malicious content inside files. Some malware hides its code inside alternate streams to avoid detection. By using the PowerShell Get-Content Stream, analysts can uncover these hidden threats.
In digital forensics, investigators use it to analyze file history and uncover hidden evidence that is not visible through standard tools.
System administrators also use the PowerShell Get-Content Stream to store configuration details or metadata without modifying the visible file content.
Security Importance
The PowerShell Get-Content Stream plays an important role in system security. While alternate data streams are not harmful by themselves, they can be misused to hide malicious content.
A file may look completely safe on the surface but still contain hidden data inside its streams. This makes it important for security professionals to inspect files carefully.
PowerShell provides direct access to these hidden streams, helping administrators ensure full system transparency.
Benefits
One of the biggest advantages of the PowerShell Get-Content Stream is its ability to provide deep visibility into file structures. It allows users to inspect hidden layers that are not visible in normal file views.
Another benefit is improved security analysis. Hidden threats can be detected more easily by examining file streams.
The PowerShell Get-Content Stream also supports automation, allowing scripts to scan multiple files and extract hidden data efficiently.
In forensic investigations, it helps uncover hidden evidence that would otherwise remain invisible.
Limitations
Despite its usefulness, the PowerShell Get-Content Stream has some limitations. It only works on NTFS file systems and may not function on other storage types.
It also requires technical knowledge, as hidden streams are not visible in standard file explorers. Additionally, most files do not contain multiple streams by default, which limits its use in simple scenarios.
Because of these factors, the PowerShell Get-Content Stream is mostly used by advanced users and professionals.
Common Misconceptions
Many users misunderstand how streams work. One common misconception is that hidden streams are separate files, but they are actually part of the same file structure.
Another misunderstanding is that hidden data is safe from deletion. In reality, when a file is deleted, all its streams are removed as well.
Some users also believe every file contains hidden streams, but this is not true. Most files only contain a single visible stream unless additional data is added manually.
Best Practices
When working with the PowerShell Get-Content Stream, it is important to follow best practices to ensure proper usage.
Security checks should always include scanning for hidden streams in unknown files. Sensitive data should not be stored in hidden streams unless necessary.
Using clear stream names helps maintain organization and reduces confusion during analysis. Proper documentation is also important when working in team environments.
Combining the PowerShell Get-Content Stream with other PowerShell tools improves overall file analysis and system visibility.
Why It Matters
The PowerShell Get-Content Stream remains highly relevant in modern IT environments. As systems become more advanced, hidden data storage methods are becoming more common.
This feature helps administrators and security professionals maintain full visibility into file contents. It ensures that no hidden data goes unnoticed in system analysis.
PowerShell continues to play a major role in Windows automation, and the PowerShell Get-Content Stream is an important part of its advanced functionality.
Conclusion
The PowerShell Get-Content Stream is a powerful feature used to access hidden data inside files through Alternate Data Streams. It provides deep insight into file structures that are not visible using standard tools.
From cybersecurity to system administration and digital forensics, it plays an important role in modern computing environments. Although it is not commonly used by everyday users, it is extremely valuable for professionals who require advanced file inspection capabilities.
Understanding the PowerShell Get-Content Stream helps improve both technical knowledge and security awareness, making it an essential concept in Windows system management.
FAQs
Q: What is PowerShell Get-Content Stream?
A: It is a PowerShell feature used to read hidden Alternate Data Streams inside files.
Q: Why is PowerShell Get-Content Stream used?
A: It is used to access hidden data, metadata, and security-related file information.
Q: Can normal users see file streams?
A: No, hidden streams are not visible in File Explorer or normal file viewing tools.
Q: Is PowerShell Get-Content Stream safe to use?
A: Yes, it is safe and commonly used for system administration and security checks.
Q: What type of files support streams?
A: Only files on NTFS file systems support Alternate Data Streams.

